- (Topic 8)
Joe Hacker is going wardriving. He is going to use PrismStumbler and wants it to go to a GPS mapping software application. What is the recommended and well-known GPS mapping package that would interface with PrismStumbler?
Select the best answer.
Correct Answer:A
Explanations:
GPSDrive is a Linux GPS mapping package. It recommended to be used to send PrismStumbler data to so that it can be mapped. GPSMap is a generic term and not a real software package. WinPcap is a packet capture library for Windows. It is used to capture packets and deliver them to other programs for analysis. As it is for Windows, it isn't going to do what Joe Hacker is wanting to do. Microsoft Mappoint is a Windows application. PrismStumbler is a Linux application. Thus, these two are not going to work well together.
- (Topic 8)
This packet was taken from a packet sniffer that monitors a Web server.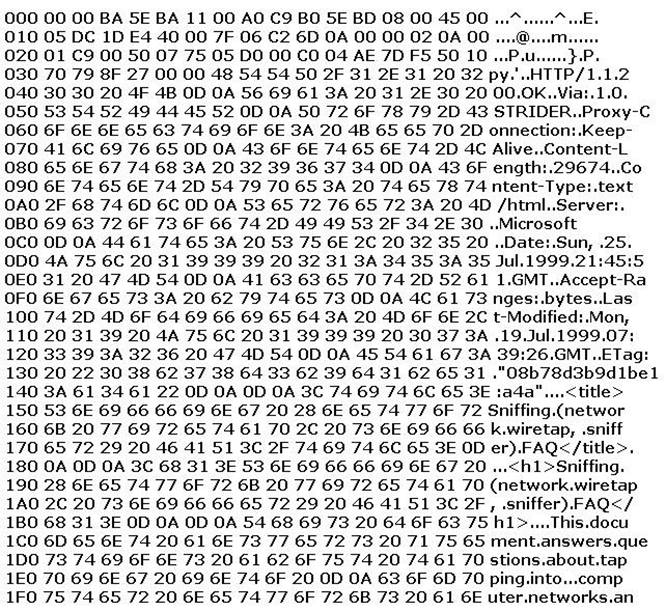
This packet was originally 1514 bytes long, but only the first 512 bytes are shown here. This is the standard hexdump representation of a network packet, before being decoded. A hexdump has three columns: the offset of each line, the hexadecimal data, and the ASCII equivalent. This packet contains a 14-byte Ethernet header, a 20-byte IP header, a 20-byte TCP header, an HTTP header ending in two line-feeds (0D 0A 0D 0A) and then the data. By examining the packet identify the name and version of the Web server?
Correct Answer:B
We see that the server is Microsoft, but the exam designer didn’t want to make it easy for you. So what they did is blank out the IIS 4.0. The key is in line “0B0” as you see:
0B0 69 63 72 6F 73 6F 66 74 2D 49 49 53 2F 34 2E 30 ..Microsoft
49 is I, so we get II 53 is S, so we get IIS 2F is a space
34 is 4 2E is . 30 is 0
So we get IIS 4.0 The answer is B
If you don’t remember the ASCII hex to Character, there are enough characters and numbers already converted. For example, line “050” has STRIDER which is 53 54 52 49 44 45 52 and gives you the conversion for the “I:” and “S” characters (which is “49” and “53”).
- (Topic 5)
A pentester is using Metasploit to exploit an FTP server and pivot to a LAN. How will the pentester pivot using Metasploit?
Correct Answer:D
- (Topic 8)
Which of the following snort rules look for FTP root login attempts?
Correct Answer:D
The snort rule header is built by defining action (alert), protocol (tcp), from IP subnet port (any any), to IP subnet port (any any 21), Payload Detection Rule Options (content:”user root”;)
- (Topic 1)
Jimmy, an attacker, knows that he can take advantage of poorly designed input validation routines to create or alter SQL commands to gain access to private data or execute commands in the database. What technique does Jimmy use to compromise a database?
Correct Answer:D